infsoft Year in Review 2023
In this blog post, we have collected all the important happenings from 2023 for you.
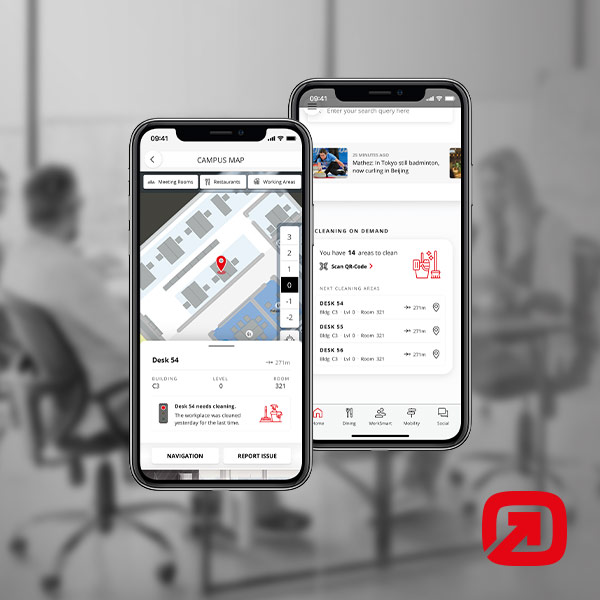
Inclusive Approaches in the Workplace Experience App
Equal opportunities through technology: The Workplace Experience App as support for inclusive work environments
infsoft Locator Node Dongle: Cost-Effective and Flexible Gateway Infrastructure
This blog post focuses on the infsoft Locator Node Dongle and its advantages as infrastructure hardware.
Q&A – Data security in the Workplace Experience App
Learn how the app uses specific procedures and measures to protect user data according to privacy policies.
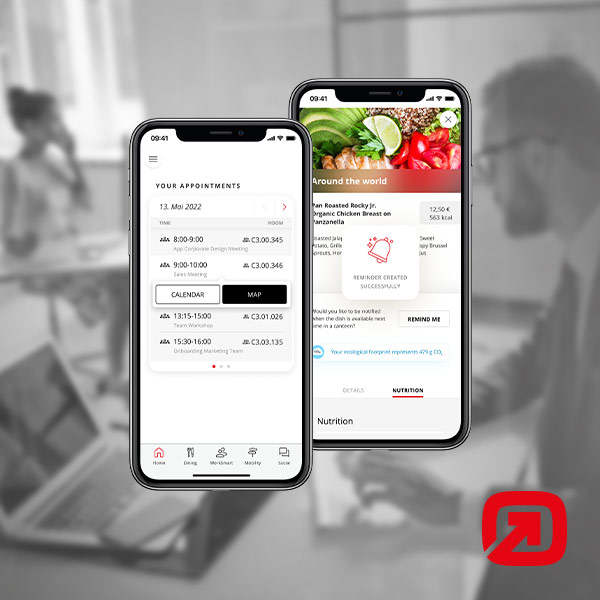
Options for customization in the Workplace Experience App
Learn more about the personalization options available within the Workplace Experience App.
Interfaces and Service Provider in the Workplace Experience App
This blog post provides additional information on interfaces and service provider integration within the Workplace Experience App.
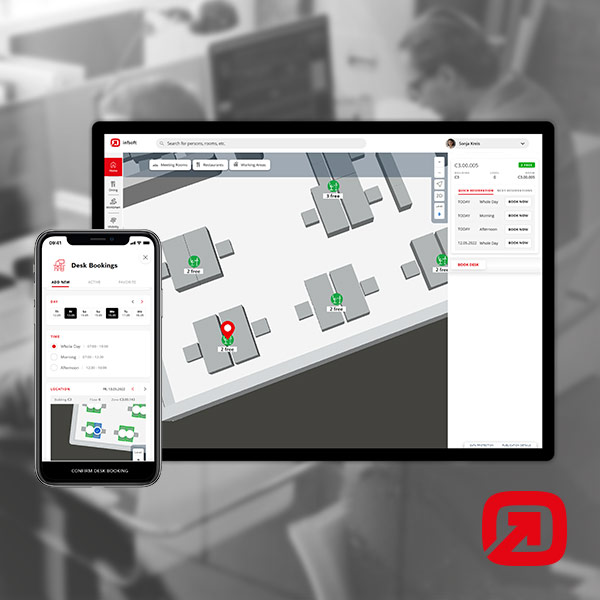
Options for Booking and Reservation in the Workplace Experience App
Various booking & reservation options in the Workplace Experience App.
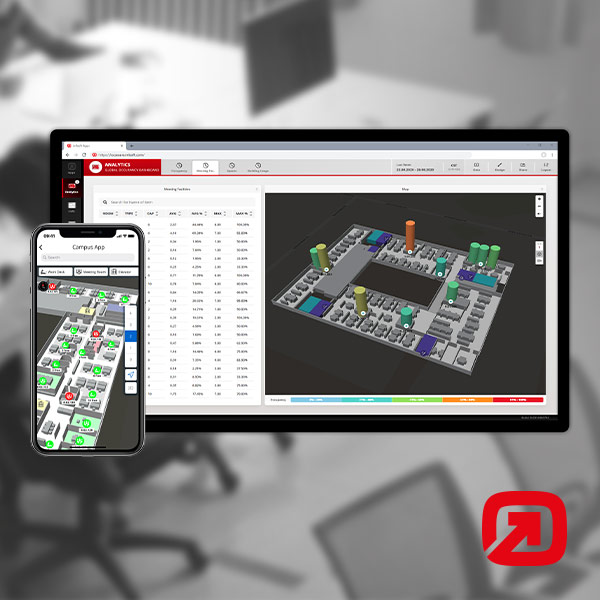
Occupancy Analytics in the Workplace Experience App
Overview of the various occupancy analytics in the Workplace Experience App.
infsoft Year in Review 2022
In this blog post, we have collected all the important happenings from 2022 for you.
Digital Transformation
Opportunities and approaches to digital transformation in four superordinate business units.